 Recently there was an encounter with a rootkit. The symptoms, open any of three different web browsers, Google Chrome, Microsoft Internet Explorer, or Mozilla Firefox and do a couple of searches, the pages would redirect several times over until finally stopping at one of many different web pages. Since, each browser was effected, it had to be a system wide problem. Malwarebytes Anti-Malware did not find this rootkit. Fortunately, Malwarebytes offers a free tool that does.
Recently there was an encounter with a rootkit. The symptoms, open any of three different web browsers, Google Chrome, Microsoft Internet Explorer, or Mozilla Firefox and do a couple of searches, the pages would redirect several times over until finally stopping at one of many different web pages. Since, each browser was effected, it had to be a system wide problem. Malwarebytes Anti-Malware did not find this rootkit. Fortunately, Malwarebytes offers a free tool that does.
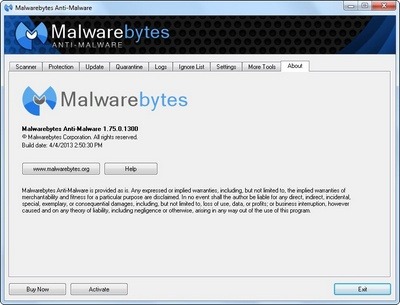
Open Malwarebytes and go to the More Tools tab. Then select Anti-Rootkit.

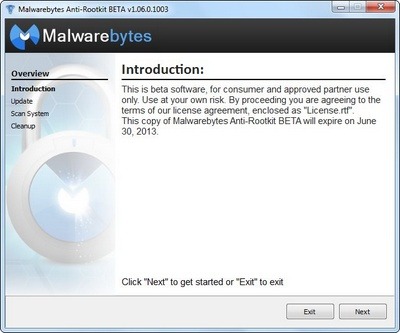
This link will open a page on Malwarebytes site to download the Malwarebytes Anti-Rootkit.

Downlad and save the zip. After extracting the zip archive, execute the mbar.exe file and follow the instructions.
From the automatically generated log file, mbar-log-YYYY-MM-DD(XX-XX-XX).txt file found in the zip extracted folder where mbar.exe exists, the following was recorded.
Folders Detected: 2
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\L (Backdoor.0Access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\U (Backdoor.0Access) -> Delete on reboot.Files Detected: 13
c:\Windows\System32\services.exe (Rootkit.0Access) -> Replace on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\@ (Backdoor.0Access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\L\00000004.@ (Backdoor.0Access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\U\00000004.@ (Backdoor.0Access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\U\00000008.@ (Backdoor.0Access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\U\000000cb.@ (Backdoor.0Access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\U\80000000.@ (Backdoor.0Access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\U\80000032.@ (Backdoor.0Access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\U\80000064.@ (Backdoor.0Access) -> Delete on reboot.
c:\Windows\assembly\GAC_32\Desktop.ini (Rootkit.0access) -> Delete on reboot.
c:\Windows\assembly\GAC_64\Desktop.ini (Rootkit.0access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\L\201d3dde (Backdoor.0Access) -> Delete on reboot.
c:\Windows\Installer\{8b3344ed-c6fd-8021-9b7f-5b2b2d4b9cb1}\L\76603ac3 (Backdoor.0Access) -> Delete on reboot.
After a reboot, the rootkit was removed.